PHP is great for being able to easily create web apps that work. The problem is that it also easy to create code with major vulnerabilities that is a mess to read and try to audit. Many times PHP is used by desktop support technicians to create apps to track department inventory, or work orders that after a few years get coopted by the rest of the company and are being used at a scale never envisioned when the technician was copy/ pasting from a dummies book to make the code work.
Related Articles
MySQL Introduction (NEW)
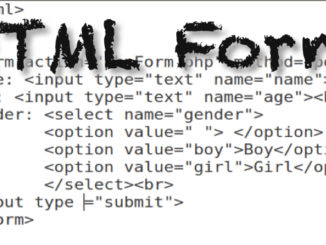
MySQL – INSERT Records with HTML Form and PHP
You can easily create an HTML form with PHP to insert records within your MySQL database. Warning – It’s important to create a troubleshooting routine, and verify you have written your code properly. form.html phpTEST.php […]
PHP Programming (NEW)
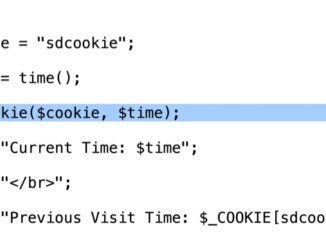
PHP – Set and Read Cookies – setcookie()
Cookies allow you to set variables that are persistent between multiple visits to a website.
PHP Programming (NEW)
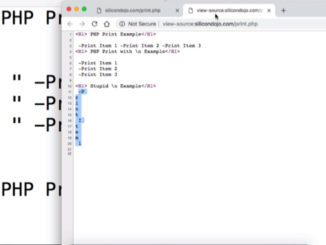
PHP – Print Function and New Line Command in…
The Print Function in PHP allows you to print text to dynamically create a web page. It’s important to understand that what you see in a web browser is different then what you would see […]
Be the first to comment